Whibox part 2: Whitebox Crypto posted August 2016
Matthieu Rivain from Crypto Experts did the transition to Whitebox Crypto.
After a bunch of funny slides about Obfuscation in general. He reminded us what were the real definitions of these new concepts.
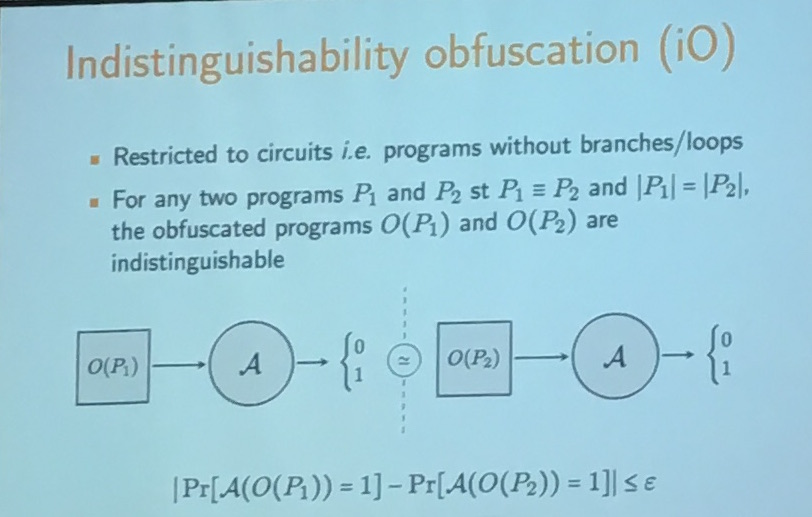
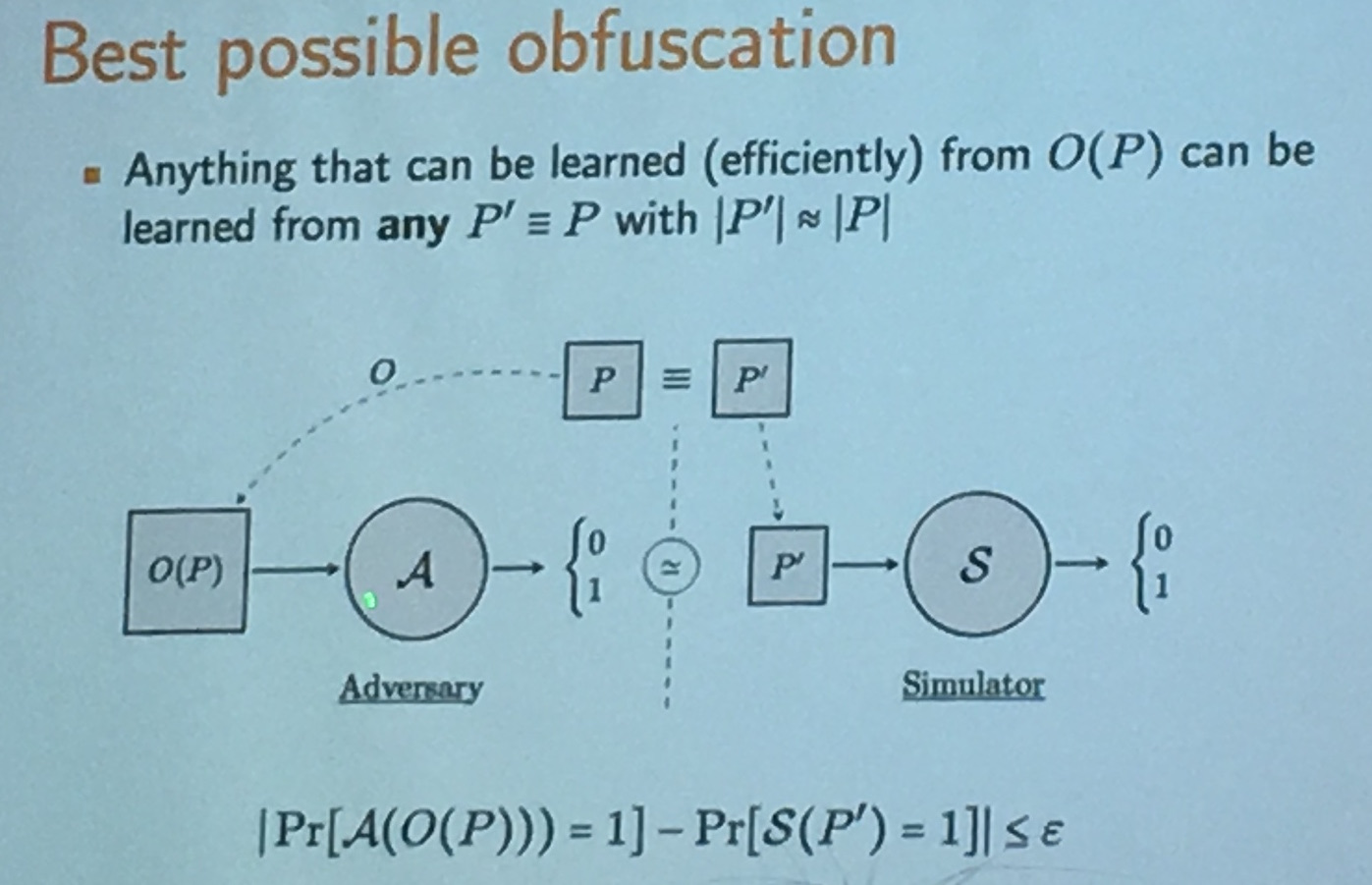
iO is equivalent to BPO, it's the best possible way to obfuscate a program. It was Chow et al. who introduced the first whitebox crypto construction in 2002 at DRM. The main goal of whitebox crypto was to make key extraction difficult, not to stop the attacker from using the program! It forces the attacker to use the software. There is value for DRM system providers.
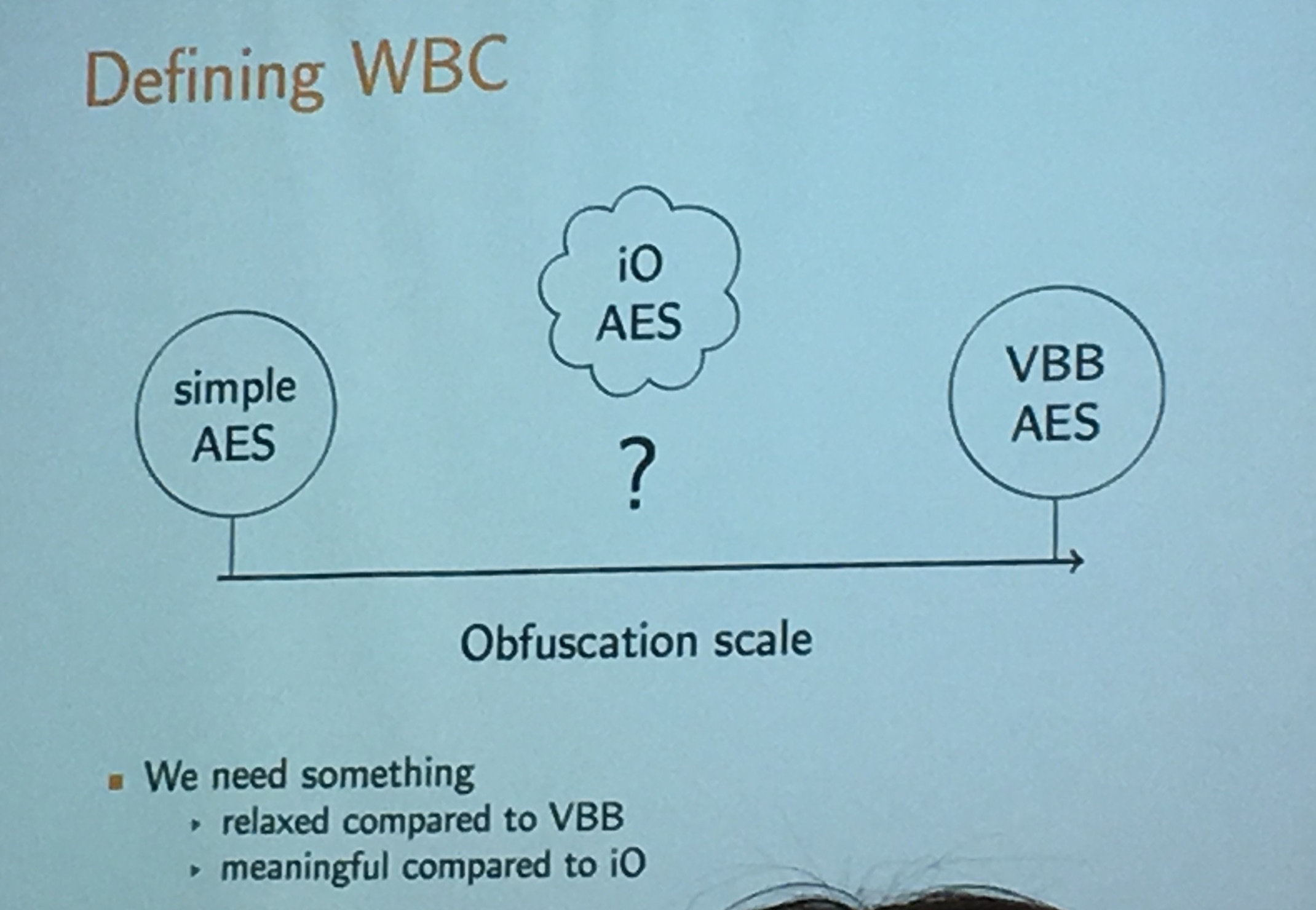
What is WBC AES? A key extraction must be "difficult".
What are the practical uses of such a scheme?
Making AES one-way and whiteboxing it turns it into a public-key cryptosystem (this is what happens in general, using whitebox on a symmetric system turns it into an asymmetric system).
There are some security notions for whitebox symmetric ciphers, the usual CPA, CCA, ... but also RCA!
RCA stands for recompilation attack: the attacker can get a new compilation of the program.
Here we have different goals for attacks:
- extract the key
- compress a whitebox implementation to make it smaller
- inverse the whitebox implementation (if it only encrypt, make it decrypt)
- be untraceable (often if you just copy the program and send it to someone else, it is true that they will be able to use it, but it might be tied to you)
whitebox crypto is about designing a compiler for an existing encryption scheme
A "one-way" compiler to be exact.
Andrey Bogdanov - Towards secure whitebox cryptography
Unlike black box models like apps in the clouds, that deal with million of requests, probably the white box model like an app on your phone is not dealing with so much. So we don't mind it being a bit slower.
Bogdanov introduced the new Host Card Emulation trend (HCE). There are a bunch of insecure hardware out there (think old Android phones) and banks want them to be able to do secure payment and all that fuss with phones and Near Field Communication (NFC). Apple did it with a secure Enclave but we can't wait for all phones to have a secure element right? So now banks are doing it in software instead with an emulated smart card in the phone. And that's what HCE is.
- In 2014, Visa and Mastercard started supporting HCE.
- In 2017, 86% of North-america point of sales, and 78% of Europe point of sales, will support NFC.
- 2/3 of shipped phones will support NFC in 2018
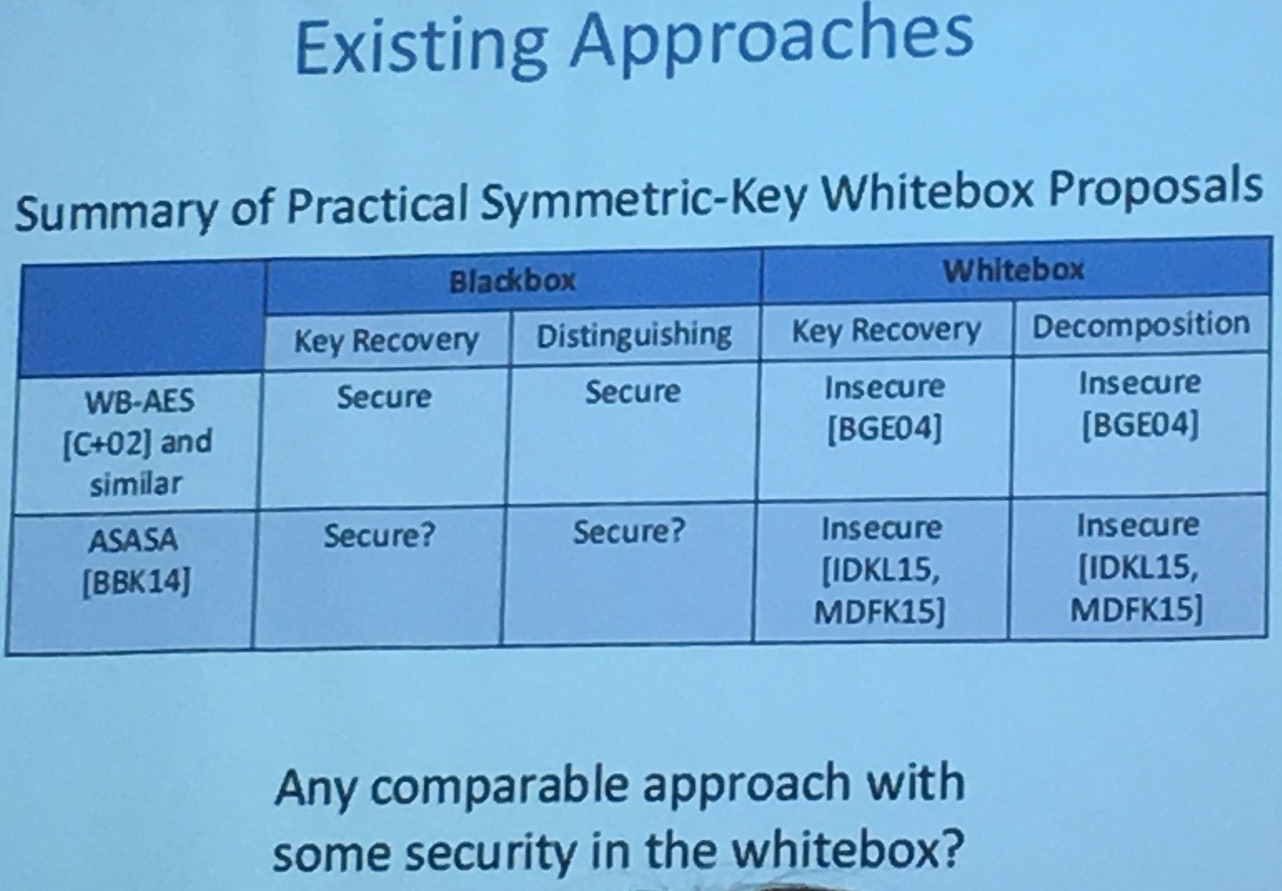
Bogdanov remarks that so far, since the first construction of Chow et al. in 2002, all Whitebox crypto schemes have been broken:
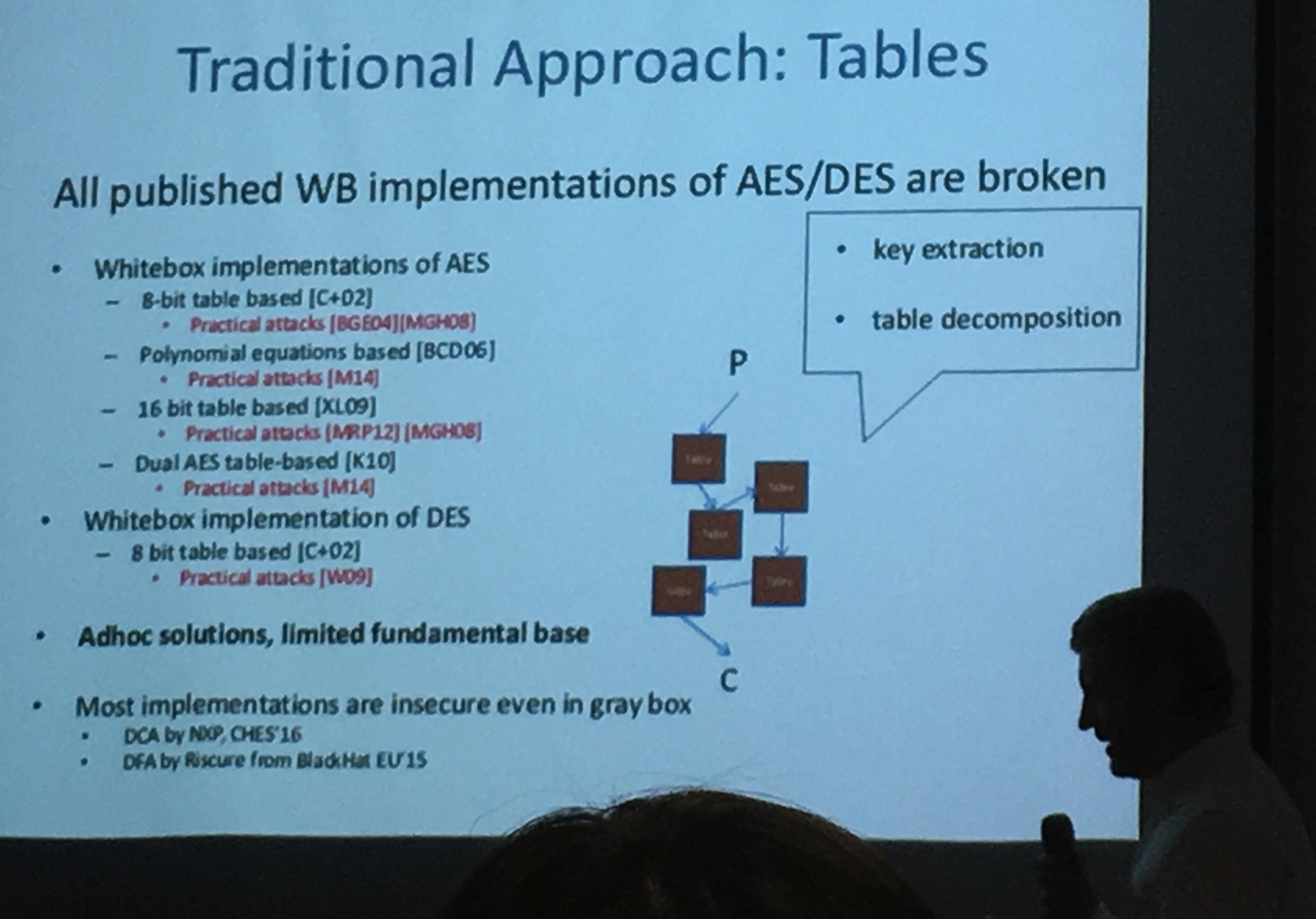
Even the recent ASASA [BBK13] in 2014 seems unsecure
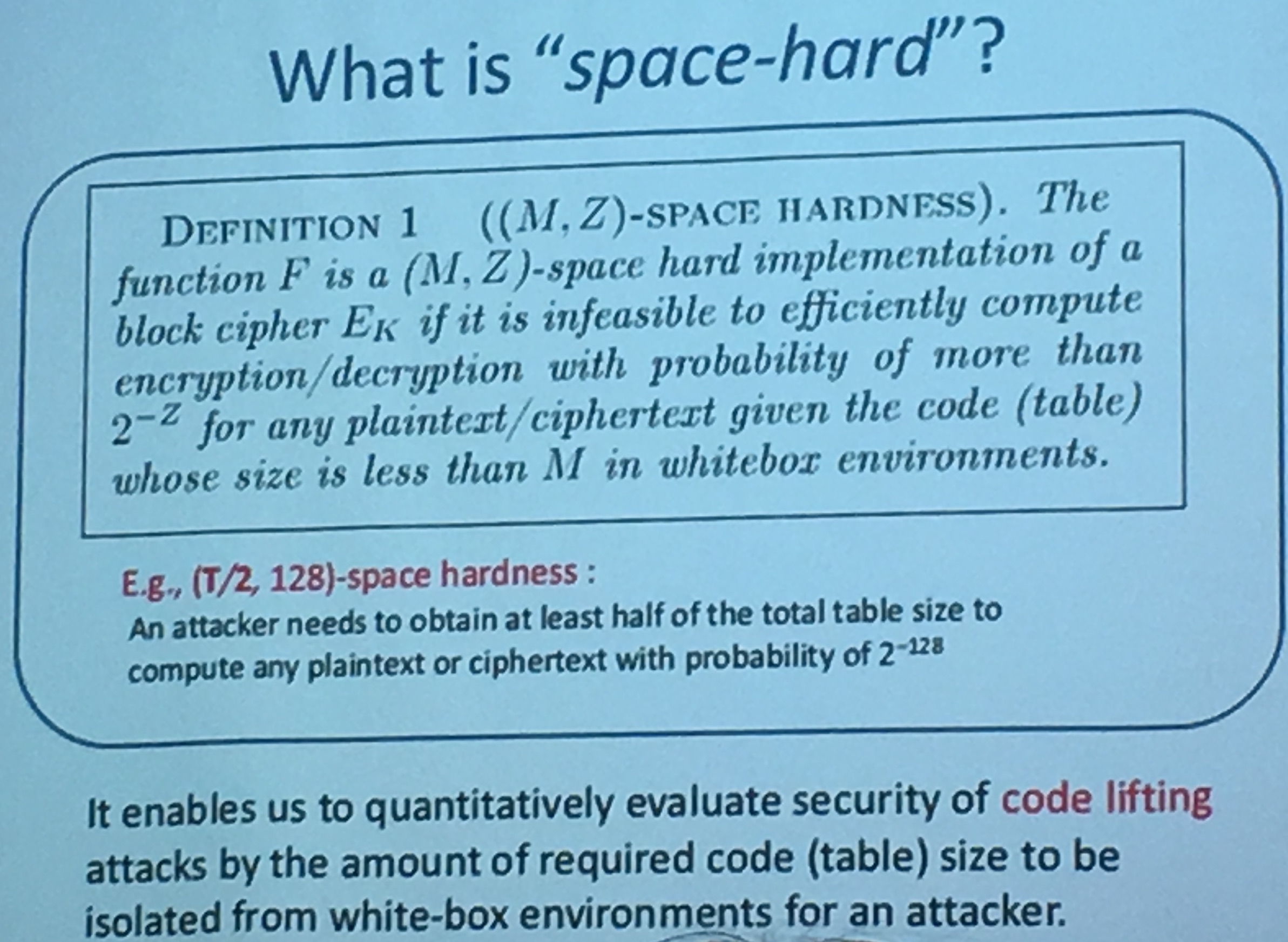
Bogdanov also adds on the security notions of whitebox crypto: *space hardness. This is the same notion M. Rivain called "compression of the whitebox". You should not be able to decompose internal component. Without all the code/tables, you shouldn't be able to compute encryption or decryption with good probability.


Comments
leave a comment...